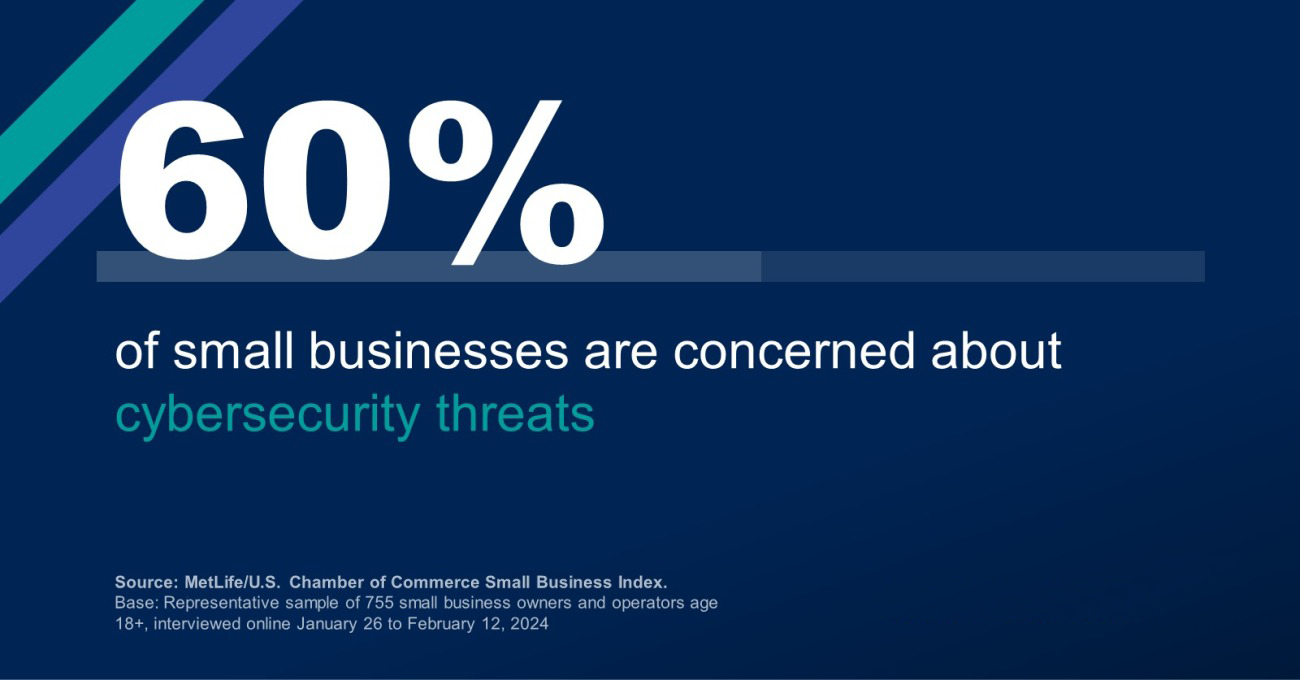
Navigating the Ever-Evolving Landscape of Cybersecurity Threats: Safeguarding Your Business in 2024
Discover the latest cybersecurity threats impacting businesses in 2024. From ransomware attacks to insider threats, learn how to safeguard your organization against evolving cyber risks. Stay informed, stay protected. #Cybersecurity #BusinessSecurity